DNS (Domain Name System) is the first point of contact between your users and your services. A DNS outage means total unavailability, regardless of the state of your application servers. That is why RDEM Systems has designed a DNS infrastructure that meets the highest standards of resilience and sovereignty.
Why DNS Is Critical
- First point of failure
If your DNS is unresponsive, your users cannot reach your services, even if your servers are running perfectly.
- Prime target for DDoS attacks
Denial-of-service attacks frequently target DNS infrastructure to maximize impact.
- NIS2 and GDPR compliance
European regulations require resilience and sovereignty of critical infrastructures.
Our DNS Architecture
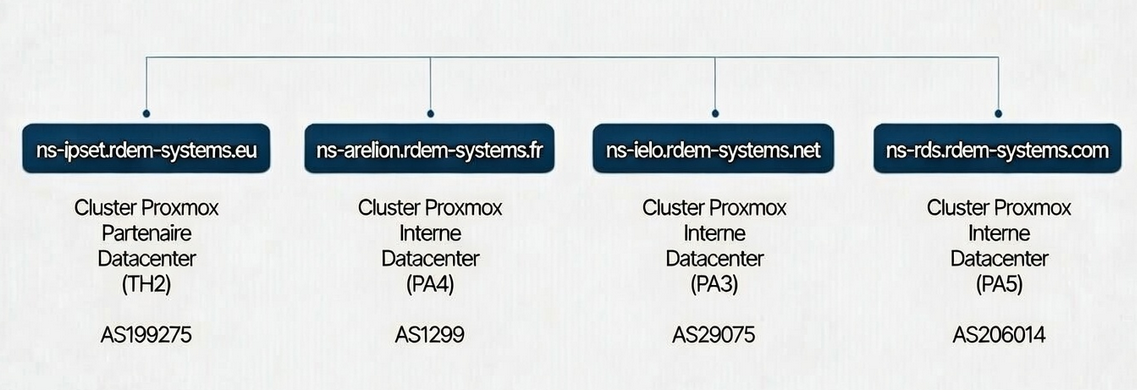
RDEM Systems operates 4 authoritative DNS servers distributed across 4 distinct ASNs (Autonomous System Numbers), hosted in 4 different datacenters in the Paris region. This diversity ensures that no Single Point of Failure (SPOF) can impact DNS resolution for our clients.
| NS Server | ASN | Datacenter | Role |
|---|---|---|---|
ns-ipset.rdem-systems.eu | AS199275 | Telehouse 2 (Paris) | IPSET, Strategic partner |
ns-arelion.rdem-systems.fr | AS1299 | Equinix PA4 (Paris) | RDEM Transit provider |
ns-rds.rdem-systems.com | AS206014 | Equinix PA5 (Paris) | RDEM own ASN |
ns-ielo.rdem-systems.net | AS29075 | Equinix PA3 (Paris) | RDEM Transit provider |
Important note: We deliberately use 4 different TLDs (.eu, .fr, .com, .net) for our NS servers. This administrative diversity follows RFC 2182 recommendations: if a TLD registry experiences an issue, the other NS servers remain accessible.
Architecture Diagram
Why This Architecture?
4 Distinct ASNs
Each NS server is announced via a different ASN (AS199275, AS1299, AS206014, AS29075). If one ASN experiences a BGP routing issue or a carrier outage, the other 3 servers continue answering DNS queries without interruption.
4 Physical Datacenters
Our servers are distributed across 4 distinct datacenters in the Paris region: Telehouse 2 (TH2), Equinix PA3, Equinix PA4, and Equinix PA5. This geographic separation protects against localized incidents (fire, power outage, severed fiber).
4 Independent TLDs
Our NS servers use 4 different extensions (.eu, .fr, .com, .net), managed by administratively independent registries. If a TLD registry encounters an issue, the other NS servers remain accessible -- in accordance with RFC 2182 recommendations.
Natural DDoS Mitigation
Distributing queries across 4 different points of presence on separate networks significantly complicates distributed denial-of-service attacks and improves latency for users.
Managed Proxmox Clusters
All our DNS servers run on Proxmox clusters that we manage directly. This control over the infrastructure guarantees total sovereignty and maximum responsiveness in case of incidents. Discover all the services hosted on our AS206014 network (fr).
DNSSEC Enabled
All our DNS zones are cryptographically signed with DNSSEC. This signature guarantees the authenticity and integrity of DNS responses, protecting against cache poisoning and man-in-the-middle attacks.
NIS2 & GDPR Compliance
This architecture meets European requirements for critical infrastructure resilience and data localization. All our servers are hosted in France.
Standards and References
Our DNS architecture is based on recommendations from the Internet's leading standards bodies:
RFC 2182 - Selection and Operation of Secondary DNS Servers
The foundational reference (IETF, 1997) that strongly recommends geographic, network (different providers/ASes), and administrative separation for secondary DNS servers. Still cited in 2026 as the basis for best practices.
Read RFC 2182APNIC Blog - DNS Nameservers: Service Performance and Resilience (2025)
Recommends at least two distinct anycast platforms (dense and diverse) to combine performance and resilience. Confirms that adding more than two anycast platforms provides diminishing marginal returns.
"Diversity and resilience [...] multiple anycast platforms can significantly improve the operational resilience."Read the APNIC article
DNS Made Easy - Multi-Network Redundancy (2025)
Explains why a single DNS backbone is not sufficient. Recommends multi-network redundancy with servers on different ASNs/providers for load balancing, DDoS mitigation, and resilience.
"Distributes DNS queries across multiple points of presence to optimize performance and minimize risk."Read the DNS Made Easy article
Catchpoint - DNS Redundancy
Emphasizes the use of multiple DNS providers on different networks (ASNs)to survive provider-specific outages or targeted DDoS attacks.
Read the Catchpoint articleValidation and Compliance
Validated via Zonemaster
Our DNS configuration is regularly tested with Zonemaster, the official tool developed by AFNIC and the Swedish registry (.SE). This tool verifies:
- Geographic and network diversity of NS servers
- DNSSEC configuration
- Compliance with IETF/AFNIC best practices
- Glue records and zone consistency
Need a resilient DNS infrastructure?
RDEM Systems can deploy and manage a similar DNS infrastructure for your organization, with the same commitment to resilience and sovereignty. See our infrastructure best practices: DNS, DNSSEC and NTP/NTS (fr).